Students must start practicing the questions from CBSE Sample Papers for Class 11 Computer Science with Solutions Set 5 are designed as per the revised syllabus.
CBSE Sample Papers for Class 11 Computer Science Set 5 with Solutions
Time Allowed: 3 hours
Maximum Marks: 70
General Instructions:
- Please check this question paper contains 35 questions.
- The paper is divided into 5 Sections- A, B, C, D and E.
- Section A, consists of 18 questions (1 to 18). Each question carries 1 Mark.
- Section B, consists of 7 questions (19 to 25). Each question carries 2 Marks.
- Section C, consists of 5 questions (26 to 30). Each question carries 3 Marks.
- Section D, consists of 2 questions (31 to 32). Each question carries 4 Marks.
- Section E, consists of 3 questions (33 to 35). Each question carries 5 Marks.
- All programming questions are to be answered using Python Language only.
Section – A
[Each question carries 1 mark]
Question 1.
CLI stands for ____. [1]
(A) Common Line Interface
(B) Command Line Interface
(C) Command Lane Interface
(D) Comment Line Interface
Answer:
(B) Command Line Interface
Explanation:
A command-line interface (CLI) is a text-based user interface (UI) used to run programs, manage computer files and interact with the computer.
Question 2.
When the result of any Boolean statement is always 0, it is known as ____. [1]
(A) True
(B) Tautology
(C) Fallacy
(D) False
Answer:
(C) Fallacy
Explanation:
An expression that always yields 0 or false is called Fallacy.
Question 3.
Base is also known as— [1]
(A) System
(B) Radix
(C) Nibble
(D) Bit
Answer:
(B) Radix
Explanation:
Base or radix: The number of distinct symbols that can be used to represent numbers in a number system is its base.
Question 4.
State TRUE or FALSE.
Expressions separated by commas are evaluated from right to left. [1]
Answer:
False
Explanation:
Two or more expressions separated by a comma are evaluated from left to right. The result is stored as a tuple
Question 5.
What would be the output of the following code snippet? [1]
print (4+9)
(A) 4+9
(B) 4 9
(C) 13
(D) Error
Answer:
(C) 13
Explanation:
It will simply add the numeric values and print the result.
Question 6.
_____ deals with the protection of an individual’s information which is implemented while using the Internet on any computer or personal device. [1]
(A) Digital agony
(B) Digital privacy
(C) Digital secrecy
(D) Digital protection
Answer:
(B) Digital privacy
Explanation:
Digital privacy is a right that seeks to guarantee the protection of the personal data of users who access a service through the Internet.
Question 7.
What is the output of print (2%6) [1]
(A) ValueError
(B) 0.33
(C) 2
(D) 2.3
Answer:
(C) 2
Explanation:
% is a modulo operator. It is used to divide the left-hand operand by right-hand operand and returns the remainder. Here, 2 is divided by 6. So the remainder is 2. Therefore the result is 2.
Question 8.
Those variables whose values can be altered after they are created and assigned are known as ____. [1]
(A) Immutable
(B) Mutable
(C) Changeable
(D) Alter
Answer:
(B) Mutable
Explanation:
Mutable data types can change their values in place e.g. Lists and dictionaries.
Question 9.
What will be the output of the following code? [1]
for i in (1,2,3):
print("A"*i)
(A) 1
2
3
(B) A * 1
A * 2
A * 3
(C) A
AA
AAA
(D) Error
Answer:
(C) A
AA
AAA
Explanation:
The ‘*’ operator acts as a replication operator and repeats the first operand number of times given by the second operand. Here, for i = 1, A prints one time, for i=2, A prints one time, for i=3, A prints one time.
Question 10.
Predict the output. [1]
str = “Application” print (str.find(”a”))
(A) 1
(B) 6
(C) Error
(D) None of these
Answer:
(A) 1
Explanation:
Here the value of a i.e. “i” is not present in the value of x i.e. “Python”. So, the loop will not execute and no output will be printed.
Question 11.
Predict the output.
str = “Application” print (str.find(a”))
(A) 1
(B) 6
(C) Error
(D) None of these
Answer:
(B) 6
Explanation:
find() function returns index of the first occurrence of an element. It is also case- sensitive.
Question 12.
What will be the output?
ls = [2, 3, 7, 8) print (sum(ls))
(A) 10
(B) 20
(C) Error
(D) None of these
Answer:
(B) 20
Explanation:
sum() function returns the addition of all elements present in the list.
Question 13.
Predict the output.
a= (1, 3, 2) *2 print (a)
(A) (1, 3, 2, 1, 3, 2)
(B) (1, 1, 3, 3, 2, 2)
(C) (2, 6, 4)
(D) (1*2, 3*2, 2*2)
Answer:
(A) (1, 3, 2, 1, 3, 2)
Explanation:
The ‘*’ operator acts as a replication operator and repeats the first operand number of times given by the second operand.
Question 14.
What will be the output of the following Python code?
a={ 1 : “One”, 2: “Two”, 3 : “Three”)
print (a.pop (5, 7))
(A) 7
(B) 5
(C) Too many arguments for pop() method
(D) One
Answer:
(A) 7
Explanation:
pop() method returns the value when the key is passed as an argument and otherwise returns the default value(second argument) if the key isn’t present in the dictionary.
Question 15.
The electronic equivalent of junk mail is known as:
(A) adware
(B) cyber fraud
(C) spam
(D) packets
Answer:
(C) spam
Explanation:
Spam is any kind of unwanted, unsolicited digital communication that gets sent out in bulk. Often, spam is sent via email, but it can also be distributed via text messages, phone calls, or social media.
Question 16.
Which of the following reduces e-waste?
(A) purchasing more and more gadgets
(B) using gadgets for a short time and then discarding
(C) good maintenance
(D) all of these
Answer:
(C) good maintenance
Explanation:
Good maintenance practices can help reduce e-waste by prolonging the lifespan of electronic gadgets.
Q17 and 18 are ASSERTION AND REASONING-based questions. Mark the correct choice as
(A) Both A and R are true and R is the correct explanation for A
(B) Both A and R are true and R is not the correct explanation for A
(C) A is True but R is False
(D) A is false but R is True
Question 17.
Assertion (A): FLOSS Source code is available Free of cost.
Reason (R): FLOSS is Open Source.
Answer:
(A) Both A and R are true and R is the correct explanation for A
Explanation:
FLOSS source code can be accessed without any cost, and FLOSS is characterized by being Open Source, which means the source code is freely available for users to view, modify, and distribute.
Question 18.
Assertion (A): Division by zero is a compile-time error.
Reason (R): Error that occurs during the execution of a program is called an exception.
Answer:
(D) A is false but R is True
Explanation:
Division by zero is a run-time error.
Section B
[Each question carries 2 marks]
Question 19.
Compare NAND and NOR gates.
OR
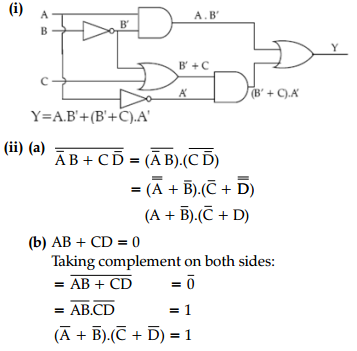
(i) Draw a logic circuit for the Boolean expression
A.B’+(C+B’).A’
(ii) Find the complement of (a) \(\overline{\mathrm{A}} \mathrm{B}\)B + \(C \bar{D}\), (b) AB + CD = 0
Answer:
| NOR Gate | NAND Gate |
| The NOR gate outputs a high (1) signal only when all inputs are low (0). | The NAND gate outputs a low (0) signal only when all inputs are high (1). |
| The NOR gate is the complement of the OR gate. | The NAND gate is the complement of the AND gate. |
OR
Question 20.
Convert 1C6A16 to
(a) Decimal
(b) Binary
Answer:
(a) 1C6A16 = ?10
1C6A16 = 1 × 163 + C × 162 + 6 × 161 + A × 160
= 1 × 4096 + 12 × 256 + 6 × 16 + 10 × 1
= 4096 + 3072 + 96 + 10
= 727410
(b) 1C6A16 = ?2
116 ⇒ 00012
C16 ⇒ 11002
616 ⇒ 01102
A16 ⇒ 10102
1C6A16 ⇒ 0011100011010102
Question 21.
Identify the type of operators?
(i) =
(ii) in
(iii) not
(iv) ==
OR
Write a Python program that accepts radius of a circle and prints its area.
Answer:
(i) Assignment operator
(ii) Membership Operator
(iii) Logical operator
(iv) Relational operator
OR
r = float(input("Enter radius of circle: "))
a = 3.14159 * r * r
print("Area of circle =", a)
Question 22.
Consider the following dictionary:
d= {‘apple’: 1, ‘pear’: 2, ‘orange’: 3}
What will be the output of the following:
(i) print(diet.fromkeys([‘mango’,’banana’], 5))
(ii) print(d.setdefault(‘apple’, 4))
(iii) print (d.popitem( ) )
(iv) d1=d.copy()
d1[‘apple’]=5
print(d)
OR
The record of a student (Name, Roll No., Marks in five subjects and percentage of marks) is stored in the following list:
stRecord = [‘Raman’, ‘A-36’, [56, 98, 99, 72, 69, 78.8].
Write Python statements to retrieve the following information from the list stRecord.
(A) Percentage of the student
(B) Marks in the fifth subject
(C) Maximum marks of the student
(D) Change the name of the student from ‘Raman’ to ‘Raghav’.
Answer:
(i) {‘mango ‘: 5, ‘banana’: 5}
(ii) 1
(iii) (‘orange’, 3)
(iv) {‘apple’: 1, ‘pear’: 2}
Explanation:
fromkeys(key, val) makes a new dictionary from the sequence provided as keys and val as their values.
setdefault(key, default_val): returns the value of the given key. If key not found, returns the default value given.
popitem() : returns the last key-value pair
copy(): makes an independent copy for the given object. Therefore changing d1 has no effect on d.
OR
(a) print(stRecord[3])
(b) print(stRecord[2][4])
(c) print(max(stRecord[2] ) )
(d) stRecord[0] = ‘Raghav’
Question 23.
Explain the following terms: [2]
(i) Associative arrays
(ii) lookup
OR
Write following expressions in Python:
(a) \(\frac{1}{3}\)b2h
(b) \(\sqrt{(x 2-x 1)^2+(y 2-y 1)^2}\)
Answer:
(i) Associative arrays: Associative arrays are data structures that map keys to values, allowing efficient retrieval based on the keys instead of numeric indices. e.g., Dictionary
(ii) Lookup: Lookup is the process of searching for a specific value or data item in a collection or data structure based on a given key or criterion.
OR
(a) 1 / 3 * b * b * h
(b) math.sqrt((x2 – x1) ** 2 + (y2 – y1) ** 2)
Question 24.
Explain two types of cookies. [2]
Answer:
Cookies can be:
- First-party cookies: These stores the user’s log in id, passwords, auto-fill information, etc. for some websites that are frequently visited.
- Third-Party cookies: These cookies are stored by websites to know your search and browsing history, analyze your preferences.
Question 25.
Rani received an SMS, from her bank querying a recent transaction. Answer the following questions as what she should do upon receiving this SMS. For each of the options, mention why or why not she should do it:
(a) Should she SMS her PIN to the given contact number? [2]
(b) Should she call the bank helpline number to recheck the validity of the SMS received?
Answer:
(a) She should not SMS her pin. If she responds by sending her PIN, then there is a chance of her bank account being hacked which can result in a huge financial loss to her.
(b) She should call the bank helpline number to recheck the validity of the SMS received since this is an act of phishing (cybercrime) which is aimed at stealthily getting information from the user.
Section C
[Each question carries 3 marks]
Question 26.
Explain the main components of the CPU. [3]
Answer:
CPU is known as the brain of the computer. It has three main components:
- Control Unit (CU): It controls and guides interpretation, flow and manipulation of data and information.
It sends control signals until the required operations are properly done by ALU and the memory unit (storage unit). - Arithmetic and Logic Unit (ALU): It performs all the required arithmetic and logical operations to perform the task.
- Memory Unit (Storage Unit): It comprises primary and secondary memory units.
Question 27.
Explain the three key attributes that are associated with any python object. [3]
Answer:
Three key attributes associated with any Python object are:
(a) Type : The type defines the behaviors and operations that can be performed on an object. type ( ) returns the type of an object.
(b) Value: The value of an object is the data in the object. print ( ) statement is used to display the value of an object.
(c) ID: The id of an object represents the location in memory of the object and does not change once it is created.
Question 28.
Write the output of the following in reference to the given string.
str = "Python Programing"
(i) print(str[-8 : -2])
(ii) print(str[4 : 10 : 2])
(iii) print(str[-1 : -1 : -1])
(iv) print(str[-2 : 4])
(v) print(str[-9 : : -3])
(vi) print(str[ : : -2])
OR
Write a program to enter and append n numbers in a list.
For example
Input: 2
Enter element at index 1: 2
Enter element at index 2: 4
Expected output Result: [‘2’, ‘4’]
Answer:
(i) ogrami
(ii) or
(iii) Nothing will print.
Reason: start index and stop index same
(iv) Nothing will print.
Reason: start index, i.e., -2 is after stop index, i.e., 4 and since a negative gap is not specified, it will not go in reverse. Hence nothing will be printed
(v) rnt
(vi) giagr otP
OR
num = []
n = int(input("How many elements you want to enter: "))
count = 1
for i in range(n):
x = input( "Enter element at index ", count,":")
count += 1
num.append(x)
print(num)
Question 29.
(i) What do you mean by nested tuple? Give an example.
(ii) Consider the given tuple and write the output of the following statements:
T1=(1, 23, 4, 5, "A", ["C", "D"], (23, 45), 45) print(len (T1)) print(T1.index(45)) print(T1.count (45)) print(T1[5] [0]*2)
Answer:
i) A tuple inside another tuple is called a nested tuple. For example:
St ((101, “Amit”,90), (107, “Anish”,85), (121, “Suman”,80))
ii) 8
7
1
CC
Question 30.
The school offers a wireless facility (wifi) to the Computer Science students of Class XI. For communication, the network security staff of the school has a registered URL schoolwifi.edu. On 17 September 2017, the following email was mass distributed to all the Computer Science students of Class XI. The email claimed that the password of the students was about to expire. Instructions were given to go to the URL to renew their password within 24 hours. [3]
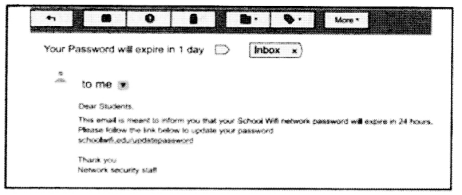
(i) Do you find any discrepancy in this email?
(ii) What will happen if the student will click on the given URL?
(iii) Is the email an example of cybercrime? If yes, then specify which type of cybercrime is it. Justify your answer.
Answer:
(i) Yes, there seems to be a discrepancy in the email, as any official action would give sufficient time for updation, rather than creating a panic hurry. Also, proper channels and authority would be asked for the same.
(ii) Clicking on a phishing link or opening an attachment in one of these messages may install malware, like viruses, spyware or ransomware, on their device.
(iii) Yes. This cybercrime is known as Phishing. This type of attack involves hackers sending malicious, but authentic-looking email attachments or URLs to users to gain access to their accounts or computer.
Section D
[Each question carries 4 marks]
Question 31.
Phishing is an unlawful activity where fake websites or emails that look original or authentic are presented to the user to fraudulently collect sensitive and personal details, particularly usernames, passwords, banking and credit card details. The most common phishing method is through email spoofing where a fake or forged email address is used and the user presumes it to be from an authentic source. [4]
(i) Phishing websites are designed to appear
(A) Official and trustworthy
(B) Suspicious and unprofessional
(C) Inaccessible and offline
(D) Educational and informative
Answer:
(A) Official and trustworthy
Phishing websites are designed to mimic legitimate websites, using similar layouts, logos, and content, to deceive users into believing they are interacting with a trusted source.
(ii) What is the primary goal of phishing attacks?
(A) Stealing personal information
(B) Spreading malware
(C) Hacking into computer systems
(D) Conducting online surveys
Answer:
(A) Stealing personal information
The main objective of phishing attacks is to trick individuals into divulging sensitive information such as usernames, passwords, credit card details, or social security numbers.
(iii) Which of the following is a common method used in phishing attacks?
(A) Malware injection
(B) IP spoofing
(C) Denial of Service (DoS)
(D) Email spoofing
Answer:
(D) Email spoofing
Phishing attacks often involve sending fraudulent emails that appear to come from a legitimate source, tricking recipients into providing sensitive information or clicking on malicious links.
(iv) True or False: Phishing attacks can target both individuals and organizations.
Answer:
True.
Phishing attacks can target both individuals and organizations, aiming to exploit vulnerabilities and gain unauthorized access to personal or sensitive information.
Question 32.
(i) Write the output of the following. [2+2=4]
import math print(math.pow(4, -2)) print(math.pow(math.sqrt(100),math.ceil(-3.96))) print(math.sqrt(math.ceil(48.10))) print(math.tan(0))
Answer:
0.0625
0.001
7.0
0.0
(ii) What are the possible outcomes(s) executed from the following code?
import random N=3 PICKER = random.randint(1, N) COLOR = ['BLUE', 'PINK', 'GREEN', 'RED'] for I in COLOR: for J in range (0, PICKER): print (I, end=' ') print ()
| (i) | (ii) | (iii) | (iv) |
| BLUE | BLUE | PINK | BLUE BLUE |
| PINK | BLUE PINK | PINK GREEN | PINK PINK |
| GREEN | BLUE PINK GREEN | GREEN RED | GREEN GREEN |
| RED | BLUE PINK GREEN RED | RED RED |
Answer:
Option (i) and (iv) are possible
The maximum value of PICKER is 3 and minimum is 1
Explanation:
The code prints all the values in COLOR, PICKER times. Now PICKER can range between 1 to 3, so i and iv options are correct. The same color will be printed together in a single line.
Section E
[Each question carries 5 marks]
Question 33.
(i) What is a flowchart? What is the use of it? [2 + 2 + 1 = 5]
(ii) What is the use of the following Row chart symbols?
(A)

(B)

(iii) Draw a flowchart to calculate the sum of two numbers and print it.
OR
(i) Write a program to print the following pattern. [4+1=5]
(a) 1
1 2
1 2 3
1 2 3 4
(b) * * * *
* * *
* *
*
(ii) Write a Python statement to display the last digit of a given number ‘num’.
Answer:
(i) A flowchart is a pictorial representation of the step by step solution of a problem.
Use of Flowchart
A flowchart depicts the flow of logic as the sequence in which instructions are carried out, in a pictorial form.
(ii)

(a) Decision box is used whenever a condition needs to be tested and the flow of the program (the next step to be executed) depends upon the result of the condition.
![]()
(b) Processing box shows the processing or calculations that are being performed.
(iii)
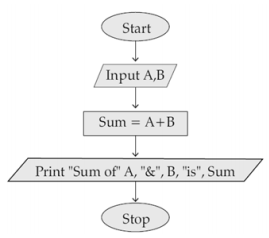
OR
(i) 1
a)
for i in range(1, 5): for j in range(1, i+1): print(j, end=" ") print( )
b)
for i in range(4, 0, -1):
for j in range(i):
print("*", end=" ")
print( )
(ii) 2
print("Last digit of number is ",num%10)
Question 34.
What does each of the following expressions evaluate to? Suppose that L is the list Eps
L = [“These”, [“are”, “a”, “few”, “words”], “that”, “we”, “will”, “use”].
(i) L[1][0::2]
(ii) “a” in L[1][0]
(iii) L[:1] + L[1]
(iv) L[2::2]
(v) L[2][2] in L[1]
Answer:
(i) [‘are’, ‘few’]
(ii) True
(iii) [‘These’, ‘are’, ‘a’, ‘few’, ‘words’]
(iv) [‘that’, ‘will’]
(v) True
Question 35.
Write a Python program to find the sum of the following series, upto n:
1 + \(\frac{x}{1 !}\) + \(\frac{x^2}{2 !}\) + \(\frac{x^3}{3 !}\) + ……. + \(\frac{x^n}{n !}\)
OR
(i) What will the following code result in? justify your answer.
L1 = [1, 3, 5, 7, 9] print (L1 == L1.reverse( ) ) print (L1)
(ii) Fill in the blanks of the following code so that the values and keys of dictionary d are inverted to create
dictionary fd. [3]
d = { 'a' :1, 'b' :2, 'c':3}
print(d)
fd = { }
for key, value in d.------- () :
fd[----------] = ----------
print(fd)
Answer:
x = int(input("Enter the value of x: "))
n = int(input("Enter the value of n: "))
sum = 0
for i in range(1, n+1):
fact = 1
for j in range(1, i+1):
fact = fact * j
sum = sum + (x**i)/fact
print("The sum of the series is: ",sum)
OR
(i) Output
False
[9, 7, 5, 3, 1]
Explanation:
L1 is not equal to its reverse so L1 = = L1.reverse( ) gives False but L1.reverse( ) reverses L1 in place so after that statement executes, L1 becomes [9, 7, 5, 3, 1].
(ii)
- items
- value
- key
The completed program is given below for reference:
d = {'a':1, 'b':2, 'c':3}
print(d)
fd = {}
for key, value in d.items():
fd[value] = key
print(fd)