Students must start practicing the questions from CBSE Sample Papers for Class 11 Computer Science with Solutions Set 2 are designed as per the revised syllabus.
CBSE Sample Papers for Class 11 Computer Science Set 2 with Solutions
Time Allowed: 3 hours
Maximum Marks: 70
General Instructions:
- Please check this question paper contains 35 questions.
- The paper is divided into 5 Sections- A, B, C, D and E.
- Section A, consists of 18 questions (1 to 18). Each question carries 1 Mark.
- Section B, consists of 7 questions (19 to 25). Each question carries 2 Marks.
- Section C, consists of 5 questions (26 to 30). Each question carries 3 Marks.
- Section D, consists of 2 questions (31 to 32). Each question carries 4 Marks.
- Section E, consists of 3 questions (33 to 35). Each question carries 5 Marks.
- All programming questions are to be answered using Python Language only.
Section – A
[Each question carries 1 mark]
Question 1.
Which of the following software is/are mandatory for all computer systems to
(A) System
(B) Application
(C) Utility
(D) Customised
Answer:
(A) System
Explanation:
System software is software designed to provide a platform for other software. Examples of system software include operating systems like Windows.
Question 2.
The complementary Law states that:
(A) X+X=X
X.X=X
(B) \(\bar{X}\) = X
(C) X + \(\bar{X}\) = 1
X.\(\bar{X}\) = 0
(D) X + Y = Y + X
X . Z = Y . Z
Answer:
(C) X + \(\bar{X}\) = 1
X.\(\bar{X}\) = 0
Explanation:
The complement is the inverse of a variable and is indicated by a bar over variable (overbar). For example, the complement of the variable A is A. If A = 1, then A = 0 and vice- versa.
Question 3.
State TRUE or FALSE.
ASCII stands for Asian Standard Code for Information Interchange.
Answer:
False
Explanation:
ASCII: American Standard Code for Information Interchange.
Question 4.
Which of the following modes in Python allows you to execute code and see the output for each statement? [1]
(A) Interactive mode
(B) Script mode
(C) Both (A) and (B)
(D) None of these
Answer:
(A) Interactive mode
Explanation:
Interactive mode in Python allows you to run code statements and instantly see the output for each statement. You can enter code directly into a Python interactive shell or interactive window and observe the output immediately after executing each statement.
Question 5.
Which of the following is a valid variable name? [1]
(A) var@
(B) 32var
(C) class
(D) abc_a_c
Answer:
(D) abc_a_c
Explanation:
Variable name should not be a keyword, cannot begin with a digit and should not contain a special symbol, except underscore ‘_’. Hence D is the correct identifier or variable, as class is the keyword.
Question 6.
Intellectual property is legally protected by [1]
(A) Copyright
(B) Patents
(C) Trademarks
(D) All of these
Answer:
(D) All of these
Explanation:
Intellectual property is legally protected by copyright, patents, and trademarks. Copyright protects creative works, patents protect inventions, and trademarks protect brands and logos. These forms of intellectual property rights provide legal protection and exclusive rights to their respective owners.
Question 7.
The ____ operator is used to add the right-hand side value to the left-hand side variable. [1]
(A) +=
(B) =+
(C) +
(D) None of these
Answer:
(A) +=
Explanation:
‘+=’ adds value on the right side to the left operand and assigns the result to the left operand. For example,
c += a is equivalent to c = c + a
Question 8.
Identify the CORRECT data type of the following variable. [1]
Age = ’49’
(A) Integer
(B) String
(C) Float
(D) Decimal
Answer:
(B) String
Explanation:
String is a consecutive sequence of characters which are enclosed in single quotes (‘ ‘) or double quotes (” “).
Question 9.
Which one of the following is a valid Python if statement: [1]
(A) if a>=2:
(B) if (a >= 2)
(C) if (a => 22)
(D) if a >= 22
Answer:
(A) if a>=2:
Explanation:
Python if statement has the syntax: if : The condition need not necessarily be in parenthesis, but a colon must be at the last to mark the starting of if block.
Question 10.
Predict the output [1]
for i in range (5): if(i%2==0) : print(i)
(A) 1
2
3
4
5
(B) 2
4
(C) 0
2
4
(D) Error
Answer:
(C) 0
2
4
Explanation:
The loop runs for values {0, 1, 2, 3, 4}. In if statement whenever i gets even value, it execute the expression inside if, i.e. prints it.
Question 11.
Given str1=”Honesty is the best policy” [1]
What will be the output of the following code?
L=len (str1) print(L)
(A) 22
(B) 26
(C) 25
(D) 24
Answer:
(B) 26
Explanation:
len( ) function returns the number of items in an object. When the object is a string, the len() function returns the number of characters in the string.
Question 12.
What will be the output of the following code?
Name=[”Ram”, “Geeta”, Priya”, Sanu”, “Pihu”, “Anuj”, “Rohit”] Name.remove (“Priya”) Name.pop (4) del Name(4] print (Name)
(A) [‘Rain’, ‘Geeta’, ‘Sanu’, ‘Pihu’, ‘Anuj’]
(B) [’Ram’, ‘Geeta’, ‘Sanu’, ‘Pihu’]
(C) [‘Ram’, ‘Geeta’, ‘Sanu’, ‘Pihu’, Anuj’]
(D) I’Ram’, ‘Geeta’, ‘Sanu’, ‘Pihu’, ‘Rohit’]
Answer:
(B) [’Ram’, ‘Geeta’, ‘Sanu’, ‘Pihu’]
Explanation:
list.remove( ) removes a given Item from a list: So ‘Priya’ is removed. list.pop() Remove an Item at a defined index: So ‘Anuj’ is removed, as it is at the 4th index, after removing ‘Priya’.
del list [index] Delete an Item from a list: Now ‘Rohit’ is removed, as it is now at the 4th index after ‘Anuj’ is removed.
Question 13.
Write the output of the following.
A = tuple(”Python”) print (A)
(A) (python)
(B) (“Python”)
(C) (‘P’ , ‘y’ , ‘t’ , ‘h’ , ‘o’ , ‘n’)
(D) None of these
Answer:
(C) (‘P’ , ‘y’ , ‘t’ , ‘h’ , ‘o’ , ‘n’)
Explanation:
When the string “Python” is passed as an argument to the tuple() function, it treats each character in the string as an individual element and creates a tuple with those elements.
Question 14.
Which one of the following is correct?
(A) In python, a dictionary can have two same keys with different values.
(B) In python, a dictionary can have two same values with different keys
(C) In python, a dictionary can have two same keys or same values but cannot have two same key-value pair
(D) In python, a dictionary can neither have two same keys nor two same values.
Answer:
(B) In python, a dictionary can have two same values with different keys
Explanation:
In a dictionary, each key must be unique, meaning you cannot have two identical keys. However, different keys can have the same value
Question 15.
Which of the following is not a type of cybercrime? [1]
(A) Data theft
(B) Forgery
(C) Damage to data and systems
(D) Installing antivirus for protection.
Answer:
(D) Installing antivirus for protection.
Explanation:
Antivirus software, originally designed to detect and remove viruses from computers, can also protect against a wide variety of threats, including other types of malicious software, such as keyloggers, browser hijackers, Trojan horses, worms, rootkits, spyware, adware, botnets and ransomware.
Question 16.
Which of the following statements is true about the IT Act in India?
(A) The IT Act stands for Information Technology Act and governs electronic transactions and digital signatures in India.
(B) The IT Act was enacted in 1995.
(C) The IT Act does not contain punishments for people violating it.
(D) The IT Act only applies to government organizations and not private entities.
Answer:
(A) The IT Act stands for Information Technology Act and governs electronic transactions and digital signatures in India.
Explanation:
The IT Act in India is a legislation that governs electronic transactions, digital signatures, and cybersecurity. It establishes rules and regulations for e-commerce, data protection, and addressing cybercrimes.
Q17 and 18 are ASSERTION AND REASONING-based questions. Mark the correct choice as
(A) Both A and R are true and R is the correct explanation for A
(B) Both A and R are true and R is not the correct explanation for A
(C) A is True but R is False
(D) A is false but R is True
Question 17.
Assertion (A): Don’t give or post any personal information online like your name, address of the school/office / home, phone numbers, age, sex, credit card details etc.
Reason (R): The information which was posted by you online can be seen by everyone who is online because the internet is the world’s biggest information exchange tool. [1]
Answer:
(A) Both A and R are true and R is the correct explanation for A
Explanation:
The Reason (R) provides a correct explanation for the Assertion (A). By refraining from sharing personal information online, individuals can reduce the risk of unauthorized access, privacy breaches, and misuse of their personal data.
Question 18.
Assertion (A): Whenever we change the value of a variable we change only the data reference and the data value that it was pointing to still remains there.
Reason (R): A variable does not store value itself rather it just points or refers a data value. [1]
Answer:
(A) Both A and R are true and R is the correct explanation for A
Explanation:
The Reason (R) provides a correct explanation for the Assertion (A) by clarifying that variables act as references or pointers to data values rather than storing the values directly.
Section B
[Each question carries 2 marks]
Question 19.
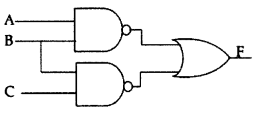
Verify the following using truth table:
U.(U’ + V) = (U. V)
OR
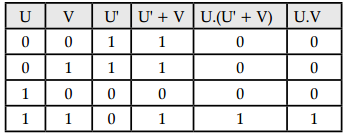
(i) Write the equivalent Boolean expression for the following logic circuit:
(ii) Write correct forms of the following boolean expression.
a) AA’ = 1
b) X + YZ = (X + Y)(X + A)
Answer:
U. (U’ + V) = (U . V)
OR
(i)
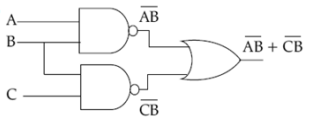
(ii) (a) A.A’ = 0
(b) X + YZ = (X + Y)(X + Z)
Question 20.
Express the following octal numbers into their equivalent decimal numbers,
(i) 6760
(ii) 10.75
OR
Encode the word ‘COMPUTER’ using ASCII and convert the encode value into binary values.
Answer:
(i) (6760)8 = 6 × 83 + 7 × 82 + 6 × 81 + 0 × 80 = (3568)10
(ii) (10.75)8 = 1 × 81 + 0 × 80 + 7 × 8-1 + 5 × 8-2 =(8.953125)10
OR
| Symbol | ASCII | Binary |
| C | 67 | 1000011 |
| O | 79 | 1001111 |
| M | 77 | 1001101 |
| P | 80 | 1010000 |
| U | 85 | 1010101 |
| T | 84 | 1010100 |
| E | 69 | 1000101 |
| R | 82 | 1010010 |
Binary code of “COMPUTER” is:
100001110011111001101101000010101011010100100
01011010010
Question 21.
Write the output of the following Python code
a = 6
b = 7
c = 42
(i) print(a == 6)
(ii) print(a == 7)
(iii) print(a == 6 and b == 7)
(iv) print(a == 7 and b == 7)
(v) print(not (a == 7) and b = = 7)
(vi) print(a==7 or b==7)
(vii) print(a==7 or b==6)
(viii) print(not(a == 7 and b == 6))
OR
Look at the following two code snippets where each code counts number of letters ‘f and ‘s’ in a sentence:
// code 1: //code 2:
if (c =='f'): if (c =='f'): nf=nf+l nf=nf+l if (c=='s'): elif (c=='s'): nf=nf+1 nf=nf+1
What is the difference between the two codes given above?
Answer:
(i) True
(ii) False
(iii) True
(iv) False
(v) True
(vi) True
(vii) False
(viii) True
Tips: Students should remember the precedence order.
OR
Code 1: Two if statements are used where each one is tested separately irrespective of the output of the former whether it is true or false, the latter will always execute.
Code 2: if-elif statement is used. In this, if the first condition becomes true then the program will not check latter conditions.
Code 1 takes more processing time.
Code 2 is more efficient.
Question 22.
Which string method is used to implement the following:
(i) To count the number of characters in the string.
(ii) To change the first character of the string to uppercase.
(iii) To check whether a given character is a letter or a number.
(iv) To change lowercase letters to uppercase.
OR
Differentiate between append () and extend () functions of the list.
Answer:
(i) len(str)
(ii) str.capitalize()
(iii) ch.isalnum()
(iv) str.upper()
OR
| append() | extend() |
| This function adds a single element passed as an argument at the end of the list. The single element can also, be a list. | This function adds all the elements of the list or any iterable sequence passed as an argument at the end of the given list. |
| For example: | For example: |
| list1=[10,20,30,40] list1.append(50) list1=[10,20,30,40,50] list1 =append([50,60]) list1 =[10,20,30,40,50, [50,60]] | list=[10,20,30] list2=[40,50] list.extend(list2) list1=[10,20,30,40,50] |
Question 23.
If a={ 1:’ abc’, 2 :’ def’ , 3 :’ ghi’, 4:’jkl’} [2]
(a) Write the statement to delete the key 3 using del command.
(b) Write the statement to delete the key 4 using the pop () function.
Also, write the dictionary state after executing each statement.
Answer:
a) del (a[3])
b) a.pop (4)
Output
{1: ‘abc’, 2: ‘def’, 4: ‘jkl’}
{1: ‘abc’, 2: ‘def’}
Question 24.
Expand the following. [2]
(A) DRM
(B) GPL
(C) EULA
(D) CC
Answer:
(a) Digital Rights Management
(b) General Public Licenses.
(c) End User License Agreement
(d) Creative Commons.
Question 25.
What was the main purpose of IT Act 2000? When were the amendments to the IT Act enforced? [2]
Answer:
Its prime purpose was to provide electronic transactions, facilitate e-governance, and promote secure and reliable electronic communication The Information Technology Amendment Act, 2008 came into force from October 27, 2009.
Section C
[Each question carries 3 marks]
Question 26.
(i) Where do we use cache memory ? [1 +2=3]
(ii) What is the largest unit of memory commonly used in computing, and approximately how many bytes does it represent?
Answer:
(i) Cache memory is used in between the CPU and the RAM and holds the most frequently used data or instructions to be processed.
(ii) The largest unit of memory commonly used in computing is the terabyte (TB). It represents approximately 1012 bytes.
Question 27.
What does sequence mean and which three types of datatypes fall into this category?
Answer:
A sequence data type is a collection of objects ordered by a specific position.
In Python, Strings, lists, and tuples are the data types based on sequences. The Sequences share common sequence operations, such as indexing, concatenation, and slicing, but also have type-specific method calls.
Question 28.
Consider the following string for subject: mySubject = “Computer Science”
What will be the output of the following string operations?
(i) print (2*mySubject)
(ii) print (mySubject [::-2])
(iii) print(mySubject[:3] + mySubject[3:])
(iv) print(mySubject. upper())
(v) print(mySubject.startswith(‘Comp’))
(vi) print(mySubject.isalpha())
OR
Write a Python program to find the list of words that are longer than n from a given list of words/ sentence.
Answer:
(i) Computer ScienceComputer Science
(ii) eniSrtpo
(iii) COMPUTER SCIENCE
(iv) cOMPUTER sCIENCE
(v) True
(vi) False
OR
n = int(input("Enter minimum length of
a word that you want to compare:"))
str=input("Enter the sentence:")
new_list = []
text = str.split(" ")
for x in text:
if len(x) > n:
new_list.append(x)
print(new_list)
Question 29.
Explain the concept of immutability in Python and what happens if we try to modify the datatype after creation.
‘Also, provide an example of an immutable data type in Python [3]
Answer:
Immutability in Python refers to the property of an object that cannot be modified once it is created. This means that any attempt to change the value or state of an immutable object will result in the creation of a new object rather than modifying the existing one. Immutable objects are preferred in scenarios where data integrity and consistency are crucial.
One of the built-in immutable data types in Python is the tuple. A tuple is an ordered collection of elements enclosed in parentheses.
Question 30.
Preeti celebrated her birthday with her family and uploaded photos on a social networking website for her friend Himanshu. After a few days, Preeti had a fight with Himanshu and deleted her birthday photographs from that social networking site, so that Himanshu cannot access them. Later, she got to know that Himanshu still had those photographs, which he recently forwarded to their common friend. [3]
Help Preeti to get answers to the following questions. Give justification for your answers so that Preeti can understand it clearly.
(a) How could Himanshu access an image which she had already deleted?
(b) Can anybody else also access these deleted images?
(c) Had these images not been deleted from her digital footprint? [3]
Answer:
(a) Himanshu must had a copy of her images before she deleted the photographs which is ethically wrong to keep.
(b) No one can access those deleted photos except Himanshu and people who have downloaded it.
(c) Deleting images from a social networking site removes them from Preeti’s profile and makes them less visible to the public. However, it’s important to understand that once something is shared online, it can potentially leave a digital footprint that is difficult to completely erase.
Section D
[Each question carries 4 marks]
Question 31.
In the code given below to calculate the sum of squares of first 10 natural numbers, find the output. Why the output is so? If the output is not correct then mark where is the error and write correct code. [4]
n=10 answer=0 while(n>0): answer=answer+n**2 n=n+1 print(answer)
Answer:
There will be no output from the given code. The while loop given in the code is an infinite loop ie., the loop will not terminate and therefore, will never execute the print Statement.
The error is in the while loop’s update condition, as the test condition will always remain True because we are increasing n every time from 10 so it will always be greater than 0.
Corrected code:
n=10 answer=0 while(n>0): answer=answer+n**2 n=n-1 print(answer)
Question 32.
Read the following case scenario and answer the subparts that follow: 1 * 4 = 4
John is a college student who is highly active on social media platforms and frequently uses the internet for various purposes. One day, while browsing the web, he unknowingly clicked on a suspicious link, which led to the installation of malware on his computer. As a result, his personal information became compromised, and he started receiving fraudulent emails asking for his banking details. Additionally, his computer was infected with ransomware, which restricted his access to important files and demanded a hefty ransom. Furthermore, John experienced cyberbullying through malicious online comments and messages.
(a) Define cyber crime in the context of the case scenario.
(b) Name and describe the process of how John’s computer became compromised in the case scenario.
(c) Explain what ransomware is and how it affected John’s computer.
(d) Explain the importance of cyber safety in relation to John’s case,
Answer:
(a) Cyber crime refers to any criminal activity that is carried out using computers or the internet. In this case scenario, cyber crime played a significant role as John’s online activities became the target of various malicious activities.
(b) In the case scenario, John fell victim to phishing through fraudulent emails. These emails posed as legitimate entities and requested his banking details. By providing his information, John unknowingly disclosed his sensitive data to cyber criminals.
(c) Ransomware is a type of malicious software that encrypts files on a victim’s computer, rendering them inaccessible until a ransom is paid. In the case scenario, John’s computer was infected with ransomware, which encrypted his important files and he had to make a ransom payment in exchange for the decryption key.
(d) Cyber safety is crucial to protect oneself while using the internet. In the context of John’s case, it involves safely browsing the web, protecting one’s identity, and maintaining confidentiality.
Section E
[Each question carries 5 marks]
Question 33.
(i) Define a pseudocode. [1+2+2=5]
(ii) Write pseudocode that will perform the following:
a. Read the marks of three subjects: Computer Science, Mathematics and Physics out of 100.
b. Calculate the aggregate marks.
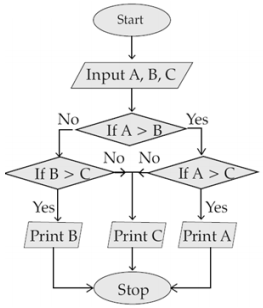
c. Calculate the percentage of marks.
(iii) Draw a flowchart to print the largest of three numbers.
Answer:
(i) The precise instructions are written in natural language using some special keywords so that the logic and flow of the program are easily understood is called a Pseudocode.
(ii)
INPUT marks of computer science (cs) INPUT marks of math (math) INPUT marks of physics (phy) COMPUTE sum = (cs + math + phy) COMPUTE percentage = (sum/300)* 100 PRINT sum PRINT percentage
(iii)
Question 34.
Write Python code that takes two parameters, “x” and “n”. The program should calculate and return the sum
of the series is defined as follows: [5]
series = x + xx + xxx + xxxx + … (up to n terms)
e.g., 3 + 33 + 333 + 3333 4- 33333, for x=3 & n=5.
OR
Write python code to calculate the sum of the series upto nth power term:
1 – x + x2 – x3 + x4 – …… xn
Answer:
x = int(input('Enter x: ')) # Value of x
n = int(input('Enter n: ')) # Number of terms in the series
series_sum = 0 # Variable to store the sum of the series
for i in range(1, n+1):
term = int(str(x) * i)
series_sum += term
print ("The sum of the series is: ", series_sum)
OR
x = int(input('Enter x: of x ')) # Value
n = int(input('Enter n: ')) # Number of terms in the series
series_sum = 0 # Variable to store the sum of the series
for i in range(n+1):
term = (-1) ** i * x ** i
series_sum += term
print("The sum of the series is: ", series_sum)
Question 35.
Write a program to convert a word into its Pig Latin format. [5]
Note: Pig Latin format is one in which the first vowel of the word is placed at the starting, and any characters/ consonants before that are moved to last, and is ended by ‘ay’, e.g., python: onpythay
OR
(i) Given strl = “Hello” and str2 = “Bye”, what is the output produced by the following expressions? [2]
(a) ” Let us all say”+ str1
(b) 3* str1 + 4 * str2
(ii) Write Python code to find the number of words in a string input by the user. [3]
Answer:
# Prompt the user to enter a word
word = input(“Enter a word: “)
vowels = [‘a’, ‘e’, ‘i’, ‘o’, ‘u’]
# Find the index of the first vowel in the word
first_vowel_index = None
for i in range(len(word)):
if word[i].lower() in vowels:
first_vowel_index = i
break
if first_vowel_index is not None:
pig_latin_word = word[first_vowel_ index:] + word[:first_vowel_index] + 'ay'
else:
pig_latin_word = word + 'ay'
# Print the converted word
print("Pig Latin: " + pig_latin_word)
OR
(i) (a) Let us all sayHello
(b) HelloHelloHelloByeByeByeBye
(ii) str1= input(” enter a string”)
words = str1.split()
print( len(words))