Students can access the CBSE Sample Papers for Class 10 Computer Applications with Solutions and marking scheme Set 9 will help students in understanding the difficulty level of the exam.
CBSE Sample Papers for Class 10 Computer Applications Set 9 With Solutions
Time Allowed : 2 Hours
Maximum Marks : 50
General Instructions :
Read thefollowing instructions carefully.
- This Question Paper has 5 Sections A-E.
- All Questions are compulsory. However, internal choices have been provided in some of the questions.
- Section A has 12 questions carrying 1 mark each.
- Section B has 7Short Answer (SA-1) type questions carrying 2 marks each.
- Section C has 4 Short Answer (SA-II) type questions carrying 3 marks each.
- Section D has 1 Long Answer (LA) type question carrying 4 marks.
- Section E has 2 Source based /Case-based /Passage based Questions carrying 4 marks each.
Section – A (12 Marks)
(All questions are compulsory)
Question 1.
Internet address is a. [1]
(a) 8 bit number
(b) 16 bit number
(c) 32 bit number
(d) None of these
Answer:
(c) 32 bit number
Explanation:
The Internet addresses comprise of 4 numbers, that is 4 × 8 = 32 bits.
Question 2.
An e-mail address is made up of : [1]
(a) Four parts
(b) Two parts
(c) Single part
(d) Three parts
Answer:
(b) Two parts
Explanation:
An Email address comprises of two parts, the username and the domain name.
Question 3.
Which of the following tag is used to add rows in the table? [1]
(a) <td> and </td>
(b) <th> and </th>
(c) <tr> and </tr>
(d) None of these
Answer:
(c) <tr> and </tr>
Explanation:
The <tr> …. </tr> tags are used to define rows of a table in HTML.
![]()
Question 4.
IP addresses of computers on a network are provided by : [1]
(a) Self Computer
(b) Network
(c) Website
(d) Both (b) and (c)
Answer:
(b) Network
Explanation:
IP address is a temporary address , provided by the network.
Question 5.
Which of the following specifies the target of an hyperlink? [1]
(a) bottom
(b) target
(c) frame
(d) Output
Answer:
(b) target
Explanation:
The target attribute is used to specify the target of a hyperlink.
Question 6.
VLINK means ____ [1]
(a) Virtual link
(b) Visited link
(c) Visual link
(d) None of these
Answer:
(b) Visited link
Explanation:
Vlink stands for visited link , the hyperlinks that have been clicked.
Question 7.
Which of the following attribute is used to provide a unique name to an element? [1]
(a) class
(b) id
(c) Type
(d) None of these
Answer:
(b) id
Explanation:
The id attribute specifies the unique name of an HTML element.
Question 8.
Which of the following is the container for <tr>, <th>, and <td>? [1]
(a) <data>
(b) < table >
(c) <group >
(d) All of these
Answer:
(b) < table >
Explanation:
The <table> tag holds the <tr> , <th> and <td> tags to specify the constituents of a table.
Question 9.
Which of the following will be an extension of an html file? [1]
(a) .htm
(b) .html
(c) .web
(d) Both (a) and (b)
Answer:
(d) Both (a) and (b)
Explanation:
HTML files are saved with extension of .html or .htm
Question 10.
Shareware are : [1]
(a) Fully paid software
(b) Free for a trial period
(c) Entirely free
(d) Open source
Answer:
(b) Free for a trial period
Explanation:
Shareware are softwares that are for free usage for a limited period of time.
![]()
Questions No-11 & 12 are Assertion and Reason types. Each question consists of two statements, namely,
Assertion (A) and Reason (R). Select the most suitable option considering the Assertion & Reason.
Question 11.
Assertion: The internet is a collection of interconnected computer networks, linked by transmission medium such as fibre optic cables, transmission wires, wireless connections, etc.
Reason: World Wide Web is a collection of websites or web pages stored in web servers and connected to local computers through the internet.
(a) Both Assertion (A) and Reason (R) are true and Reason (R) is a correct explanation of Assertion (A).
(b) Both Assertion (A) and Reason (R) are true but Reason (R) is not a correct explanation of Assertion (A).
(c) Assertion (A) is true and Reason (R) is false.
(d) Assertion (A) is false and Reason (R) is true.
Answer:
(b) Both Assertion (A) and Reason (R) are true but Reason (R) is not a correct explanation of Assertion (A).
Explanation:
The internet is the biggest network of computers and network devices . The world wide web or www comprises of web sites and web pages.
Question 12.
Assertion (A): Every <a> tag usage must have a target attribute specified.
Reason (R): If target attribute is not specified , by default the same window is used as the target.
(a) Both Assertion (A) and Reason (R) are true and Reason (R) is a correct explanation of Assertion (A).
(b) Both Assertion (A) and Reason (R) are true but Reason (R) is not a correct explanation of Assertion (A).
(c) Assertion (A) is true and Reason (R) is false.
(d) Assertion (A) is false and Reason (R) is true.
Answer:
(d) Assertion (A) is false and Reason (R) is true.
Explanation:
The target attribute may not be specified in hyperlinks as, by default the same window is used as the target.
Section – B (14 Marks)
Question 13.
What is e-Learning? Mention any main benefits of e-Learning with respect to the use of Information Technology. [2]
Answer:
Learning with the help of electronic resources like computers tablets smart phone internet etc. is known as e-Learning.
Advantages of e-Learning are:
- It is time saving as well as removes the distance barrier between learner & teacher.
- It has quicker delivery cycle times than traditional class room-based instruction. It is less expensive to set-up an e-learning environment.
Question 14.
Distinguish between MAC address and IP address with the help of example of each. [2]
OR
List some advantages of blogs.
Answer:
| Mac Address | IP Address |
| Mac Media Access Control address | IP Internet Protocol address |
| Its a 12 digit hexadecimal number assigned to each network interface card | Its a numerical label that is assigned to a device participating in a computer network |
| Can never be changed | Can be changed |
| Ex: 00 : A0: C9: 14 : C8: 35 | Ex: 192. 168.0.2 |
OR
Advantages of Blog:
(a) Blog sites can be developed with the help of simple procedures.
(b) A blog can be read by anyone.
(c) It improves writing skills of blogger.
(d) It allows us to get feedback on our thoughts.
Question 15.
What are the different types of newsgroups? [2]
Answer:
The major types of news groups are:
(i) Standard news groups: These include high quality discussions which cannot be established without a formal voting procedure.
(ii) A lt News groups: These include the discussions which can be established by anyone with the requisite technical knowledge.
Question 16.
What is a Patent? [2]
OR
What is freedom of information?
Answer:
A patent in an exclusive right granted by a country to the owner of an invention to make, use, manufacture and market the invention, provided the invention satisfies certain conditions stipulated in the law.
OR
Freedom of information refers to a citizen’s right to access information that is held by the government. The right to information is a fundamental right. It helps in creating a more open and democratic society, challenging corruption and enhancing transparency
![]()
Question 17.
Identify the errors and write the correct HTML code. [2]
(a) Identify the error in the following HTML code. Rewrite the correct code.
<UL TYPE = “a” START = 4>
(b)
<OL type=”Disc”>
<ListItem> Science</Listitem>
<ListItem> Commerce</Listitem>
<ListItem> Humanities</Listitem> ‘
</OL>
Answer:
(a) <OL TYPE=”a” START=”4”>
(b)
<UL type=”Disc”>
<LI> Science</LI>
<LI> Commerce</LI>
<LI> Humanities</LI>
</UL>
Question 18.
Match the terms/tags/attributes in column A with ones in column B [2]
| Column-A | Column-B |
| (a) target | (i) <body> |
| (b) line break | (ii) <P> |
| (c) align | (iii) <BR> |
| (d) alink | (iv) <a> |
OR
What is the use of START attribute used in lists?
Answer:
(a) – iv, (b) – iii, (c) – ii, (d) – i.
OR
The START attribute is used to change the beginning value of an ordered list. Normally, the ordered list starts with 1.
example, <OL START=”5”> </OL>
Question 19.
Write a suitable HTML statement to display the following text on a webpage in appropriate subscript and superscript form: [2]
(a)O2
(b) X² + Y²
Answer:
(a) O<sub>2</sub>
(b) X<sup>2</sup>+Y<sup>2</sup>
Section – C (12 Marks)
Question 20.
Use a definition list to show that the word “glunch” means “a look of disdain, anger, or displeasure” and that the word “glumpy” means “sullen, morose, or sulky.” [3]
Answer:
<html> <head> <title> example </title> </head> <body> <DL> <DT>glunch </DT> <DD>a look of disdain, anger, or displeasure </DD> <DT>glumpy </DT> <DD>sullen, morose, or sulky </DD> </DL> </body> </html>
Question 21.
Write an HTML code to form a table to show the below values in a tabular form with heading as Roll No., Student name, Subject Name, and values are as follows: [3]
1. Ram, Physics
2. Shyam, Math
3. Murli, Chemistry
Answer:
<html> <body> <table border=2> <tr> <th> Roll No. </th> <th> Student Name </th> <th> Subject Name </th> </tr> <tr> <td> 1 </td> <td>Ram</td> <td> Physics </td> </tr> <tr> <td> 2 </td> <td> Shyam </td> <td> Math </td> </tr> <tr> <td> 3 </td> <td> Murli </td> <td> Chemistry </td> </tr> </table> </body> </html>
![]()
Question 22.
Rishita has just created a web page to collect different travel videos link in her web page by using images of place. She wants if any user visits her web page and clicked any image then related video will be opened or played. Suggest her one example of coding to doing the same. [3]
OR
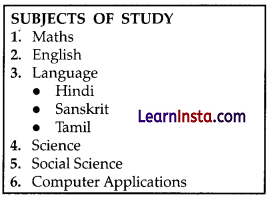
Write HTML code to design the content of the web page in the form of lists as shown below:
Answer:
<html> <head> <title> example </title> </head> <body> <a href = "https://www.youtube.com/watch?v=J7nmPBAE2X8"> <imgsrc ="QutbMinar.jpg" alt = “QutubMinar_Video”> </a> </body> </html>
OR
<HTML> <HEAD> </HEAD> <BODY> <h4>SUBJECTS OF STUDY</h4> <ol> <li> Maths <li> English <li> Language <ul type=”circle”> <li> Hindi <li> Sanskrit <li> Tamil </ul> <li> Science <li> Social Science <li> Computer Applications </ol> </BODY> </HTML>
Question 23.
How can someone improve privacy concerns in e-commerce? [3]
Answer:
There are some following ways to improve privacy concerns:
- Awareness: Give consumer’s notice of an entity’s information practices before any personal information is collected from them.
Choice/Consent: Give consumers option as to how any per sonal information collected from them may be used. - Participation: Give consumers the ability to access data about themselves i.e. to view the data in a entity’s files and to contest that data’s accuracy and completeness.
- Security: Ensure that consumer data is accurate and secure. To reassure data integrity, collectors must take reasonable steps, such as using only reputable sources of data and cross-referencing data against multiple sources.
- Security involves both managerial and technical measures to protect against multiple sources. Security involves both managerial and technical measures to protect against loss and the unauthorized access, destruction, use, or disclosure of the data.
Section – D (4 Marks)
Question 24.
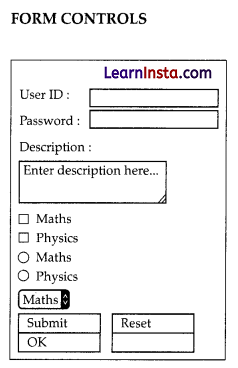
Write HTML code to create the following form. [4]
OR
Write the code to generate below table in HTML.
| A | B | C | D |
| B | D | F | H |
Answer:
<html> <head> <title>Password Input Control</title> </head> <body> <H4> FORM CONTROLS </H4> <form >User ID : <input type=”text” name=”user_id”/> <br> Password: <input type=”password” name=”password”/> <br> Description : <br /> <textarea rows=”5” cols=”50” name=”description”> Enter description here... </textarea> <br> <input type=”checkbox” name=”maths” value=”on”> Maths <br> <input type=”radio” name=”subject” value=”maths”> Maths <input type=”radio” name=”subject” value=”physics”> Physics <br> <select name=”dropdown”> <option value=”Maths” selected>Maths</option> <option value=”Physics”>Physics</option> </select> <br> <input type=”submit” name=”submit” value=”Submit” /> <input type=”reset” name=”reset” value=”Reset” /> <input type=”button” name=”ok” value=”OK” /> <input type=”image” name=”imagebutton” src=”/html/ images/logo.png” /> </form> </body> </html>
OR
<html> <body> <table border=”1” > <tr> <td> A </td> <td> B </td> <td> D </td> <td> F </td> <td> H </td> </tr> </table </body> </html>
![]()
Section – E (8 Marks)
Question 25.
Ananya is a freelancer. She used to post different works on the Internet. After that she heard of blog. She had some queries regarding blog. Solve her the following queries.
(a) What is a blog? [1]
Answer:
Blog is an online journal where an individual, group, or corpo ration presents a record of activities, thoughts, or beliefs.
(b) Name some free blogging sites. [1]
Answer:
Some of the free blogging sites are : Word Press, Linked In, Blogger, Tumblr
(c) What are the different types of blogs? [1]
Answer:
The types of blogs are:
- Personal blogs.
- Business blogs.
- Travel blogs.
- Food blogs.
- Photography blogs.
- Fashion blogs
(d) How she can be a successful blogger? [1]
Answer:
She must have good writing skills.
Question 26.
Sumit wants to clarify certain doubts regarding security concerns in e-Commerce. Help him in his queries regarding blog. Solve her the following queries.
(a) What is understood by the term Fraud? [1]
Answer:
Fraud is an intentional false representation of a fact.
(b) What are the different forms in which Fraud comes? [1]
Answer:
Fraud comes in many forms like,
- Credit card fraud
- Refund fraud
- Card testing
- Friendly fraud
- Identity theft
- Phishing
- Triangulation fraud
(c) What is understood by the term Computer ethics? [1]
Answer:
Computer ethics are a set of moral standards that govern the use of computers. It is society’s views about the use of computers, both hardware and software.
(d) What are the different Privacy concerns? [1]
Answer:
Different Privacy concerns are:
- Hacking: It is unlawful intrusion into a computer or net work. A hacker can intrude through the security levels of a computer system or network and can acquire unauthorised access to other computers.
- Malware: It means malicious software which is created to impair a computer system. Common malware are viruses, spy ware, worms, trojan horses etc. A virus can delete files from a hard drive, while a spyware can collect data from a computer.
- Data Protection: Also known as information privacy or privacy, it is the process of safeguarding data which intends to influence a balance between individual privacy rights, while still authorizing data to be used for business purposes.
- Anonymity: It is a way of keeping a user’s identity masked through various applications.